DVWA DOM XSS Exploit ( Bypass All Security)
Por um escritor misterioso
Last updated 20 junho 2024

In this article I have demonstrated how to exploit DOM-based XSS vulnerability in DVWA web application at low, medium and high security level.
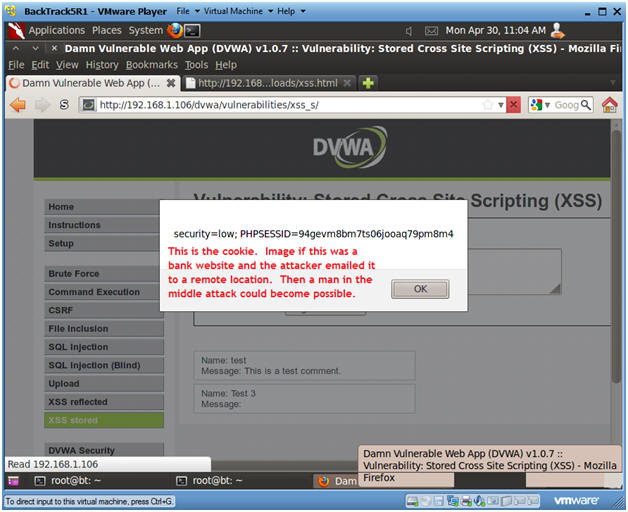
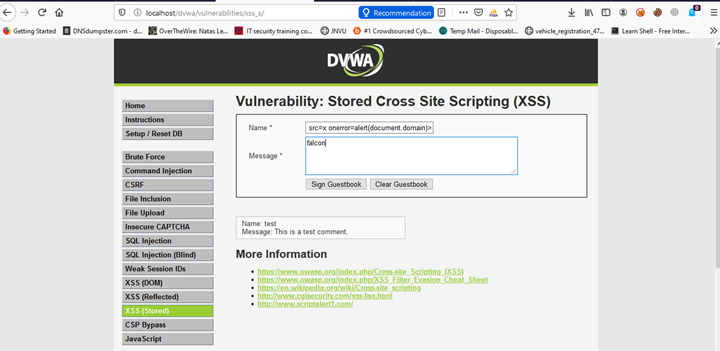
Damn Vulnerable Web App (DVWA): Lesson 9: Cross Site Scripting (XSS)

How to exploit DOM XSS on DVWA - StackZero

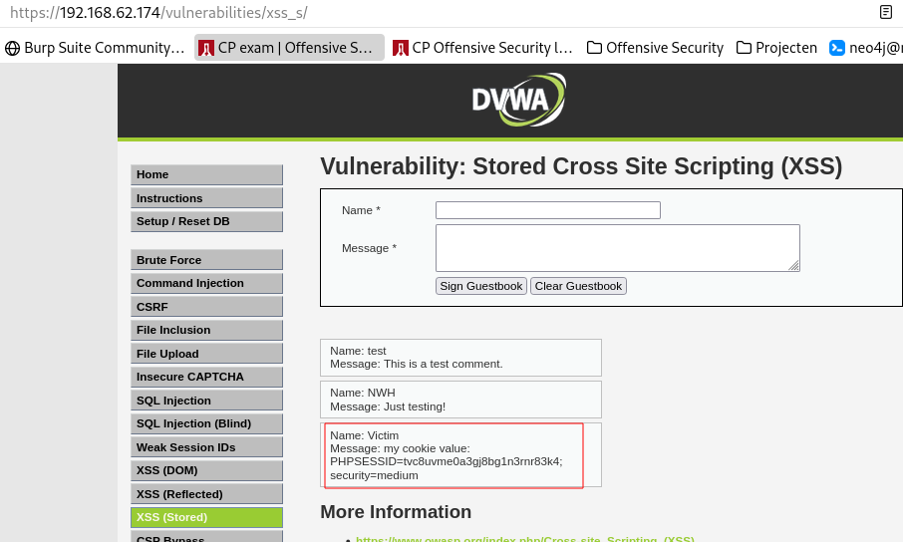
Stored Reflected and DOM Based XSS Exploitation in DVWA
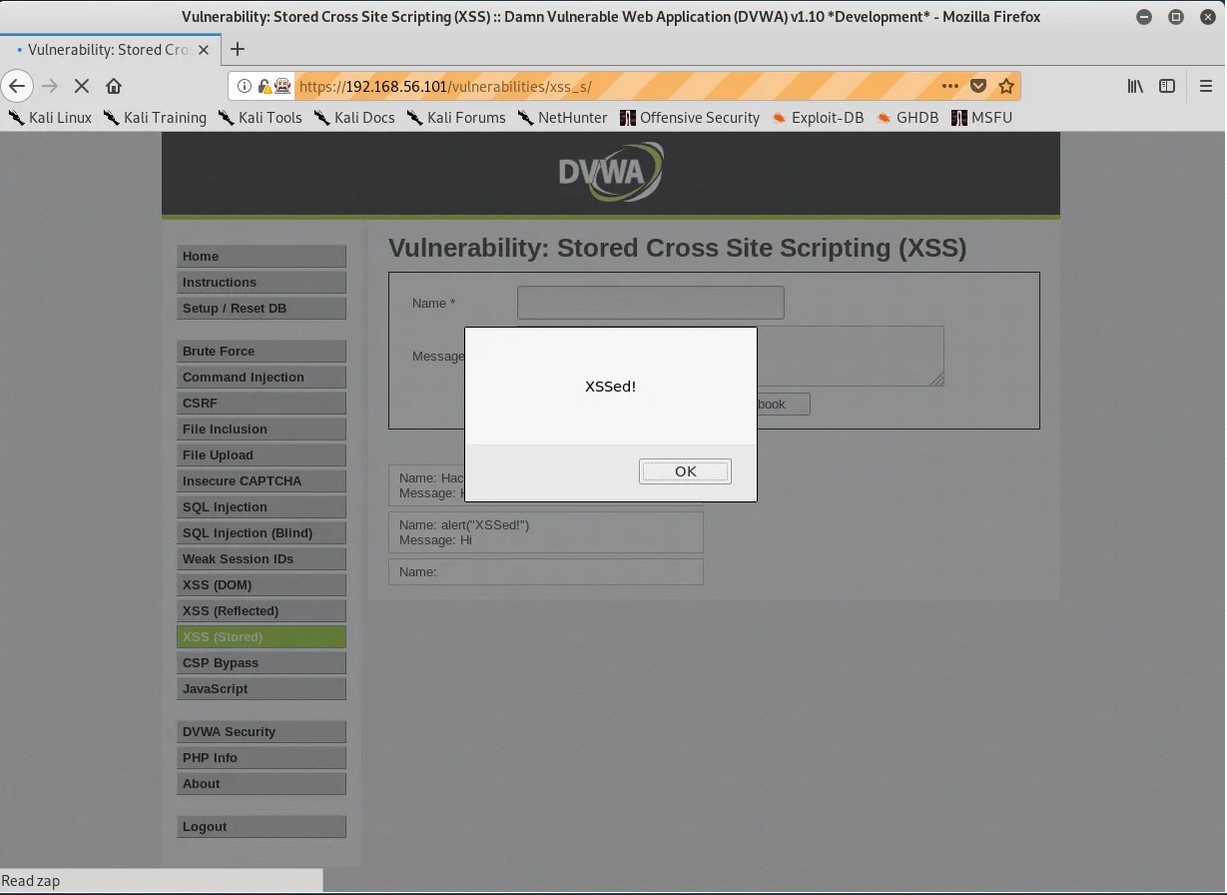
Cross Site Scripting (XSS) for Beginners - Hackercool Magazine
Cross Site Scripting(XSS) DVWA(Damn Vulnerable Web Applications

Reflected XSS DVWA - An Exploit With Real World Consequences
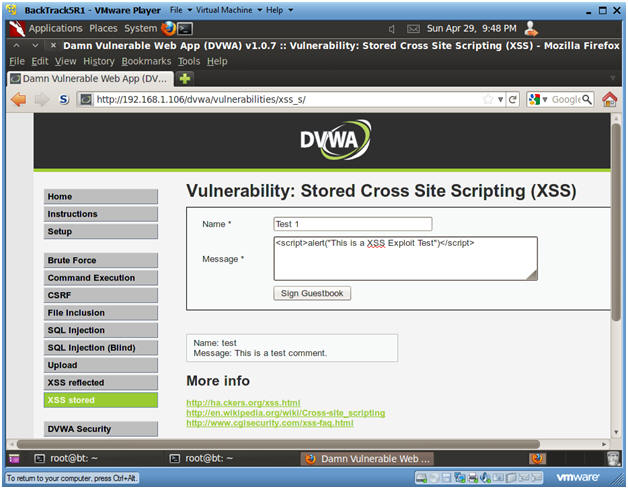
Damn Vulnerable Web App (DVWA): Lesson 9: Cross Site Scripting (XSS)

OWASP TOP 10: XSS (DOM) Attack - DVWA

Dvwa Reflected XSS Exploit
XSS exploitation without using the