Malware analysis Malicious activity
Por um escritor misterioso
Last updated 05 junho 2024

Top 10 Types of Information Security Threats for IT Teams

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis Benefits Incident Response
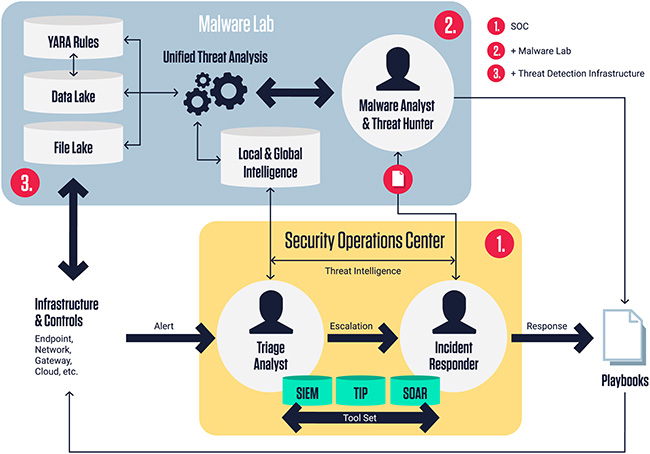
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security

Playbook for Malware outbreak

TryHackMe Cyber Security Exercises and Labs

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Malware analysis CQChallenge5.zip Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug
Lab 6-1 Solutions - Practical Malware Analysis [Book]
Recomendado para você
-
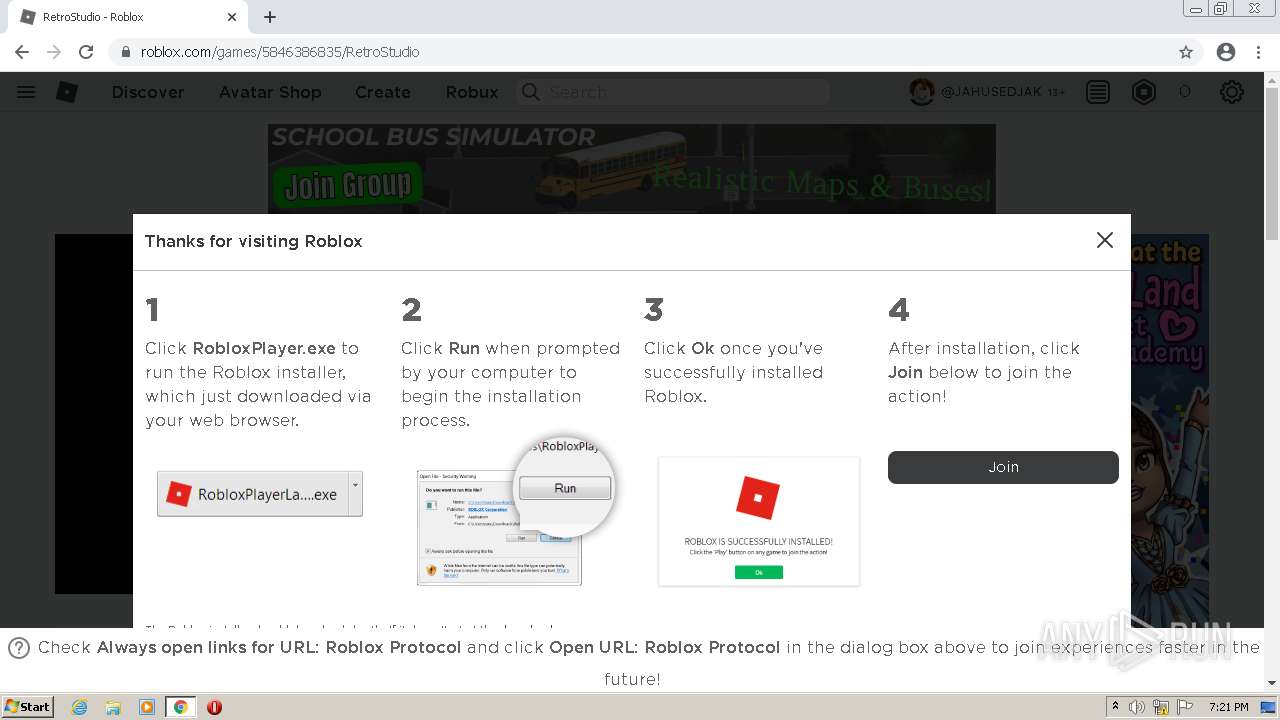
 How to Fix / Solve RobloxPlayerBeta.exe Entry Point Not Found - SarkariResult05 junho 2024
How to Fix / Solve RobloxPlayerBeta.exe Entry Point Not Found - SarkariResult05 junho 2024 -
 Bug - RobloxPlayerBeta.exe never stops - Engine Bugs - Developer Forum05 junho 2024
Bug - RobloxPlayerBeta.exe never stops - Engine Bugs - Developer Forum05 junho 2024 -
 Stream Descargar Roblox Player.exe from PerfsubPapta05 junho 2024
Stream Descargar Roblox Player.exe from PerfsubPapta05 junho 2024 -
robloxplayer-exe · GitHub Topics · GitHub05 junho 2024
-
 where is player exe|TikTok Search05 junho 2024
where is player exe|TikTok Search05 junho 2024 -
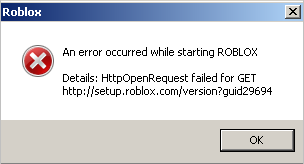 robloxplayer.exe error. : r/PhantomForces05 junho 2024
robloxplayer.exe error. : r/PhantomForces05 junho 2024 -
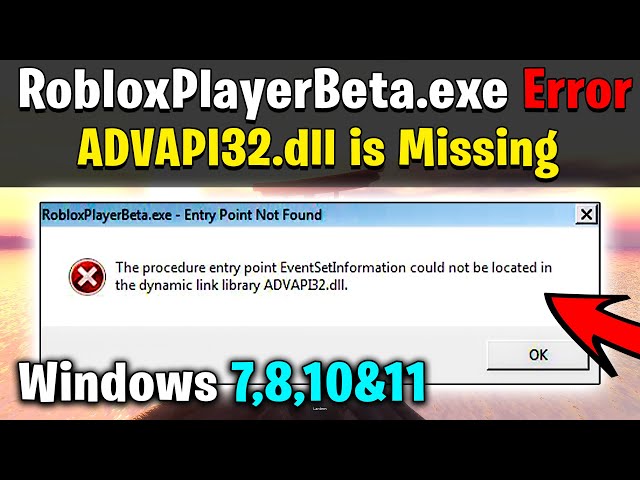 RobloxPlayerBeta.exe Error (ADVAPI32.dll is Missing) in Windows 7!05 junho 2024
RobloxPlayerBeta.exe Error (ADVAPI32.dll is Missing) in Windows 7!05 junho 2024 -
![How to Play Roblox on a Chromebook [Step by Step] - Alvaro Trigo's Blog](https://alvarotrigo.com/blog/assets/imgs/2022-08-06/search-roblox.jpeg) How to Play Roblox on a Chromebook [Step by Step] - Alvaro Trigo's Blog05 junho 2024
How to Play Roblox on a Chromebook [Step by Step] - Alvaro Trigo's Blog05 junho 2024 -
 RobloxPlayer.exe File Download Officially Updated for PC & Laptop05 junho 2024
RobloxPlayer.exe File Download Officially Updated for PC & Laptop05 junho 2024 -
 Unable to launch roblox from browser - Platform Usage Support - Developer Forum05 junho 2024
Unable to launch roblox from browser - Platform Usage Support - Developer Forum05 junho 2024
você pode gostar
-
A man with a goatee and a turtle neck sweater photo – Man face05 junho 2024
-
 The NEW ROBLOX Space Design – ROBLOX Space – A ROBLOX Blog05 junho 2024
The NEW ROBLOX Space Design – ROBLOX Space – A ROBLOX Blog05 junho 2024 -
![MUGEN Request [1705]: Ball Lock & Red Bird vs. Retro Suika](https://i.ytimg.com/vi/UIt1ND7HjNs/hq720.jpg?sqp=-oaymwE7CK4FEIIDSFryq4qpAy0IARUAAAAAGAElAADIQj0AgKJD8AEB-AH-CYAC0AWKAgwIABABGHIgWig8MA8=&rs=AOn4CLDz9gwot2E8uFRr_yPzjFcMKfKhwQ) MUGEN Request [1705]: Ball Lock & Red Bird vs. Retro Suika05 junho 2024
MUGEN Request [1705]: Ball Lock & Red Bird vs. Retro Suika05 junho 2024 -
 Bubble Gum Simulator codes in Roblox: Free Luck and Speed (June 2022)05 junho 2024
Bubble Gum Simulator codes in Roblox: Free Luck and Speed (June 2022)05 junho 2024 -
 Netflix Animated Series The Cuphead Show! Looks Like an Old05 junho 2024
Netflix Animated Series The Cuphead Show! Looks Like an Old05 junho 2024 -
 Pelly-Ruddock Mpanzu: o médio que subiu da quinta divisão até à Premier League pelo Luton Town05 junho 2024
Pelly-Ruddock Mpanzu: o médio que subiu da quinta divisão até à Premier League pelo Luton Town05 junho 2024 -
 Link to the past.Best Zelda Game05 junho 2024
Link to the past.Best Zelda Game05 junho 2024 -
 DORMIR MAIS NO FINAL DE SEMANA RECUPERA AS NOITES PERDIDAS?05 junho 2024
DORMIR MAIS NO FINAL DE SEMANA RECUPERA AS NOITES PERDIDAS?05 junho 2024 -
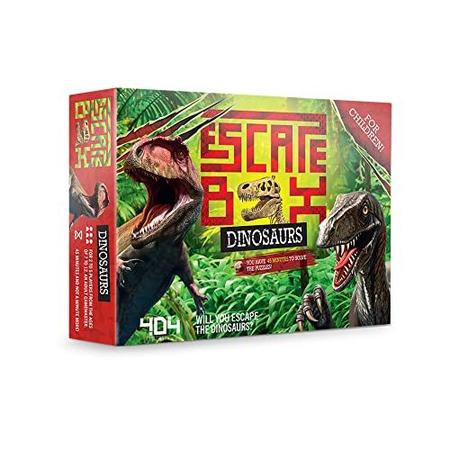 404 na Board Escape Box Dinosaurs Quarto em uma diversão para o05 junho 2024
404 na Board Escape Box Dinosaurs Quarto em uma diversão para o05 junho 2024 -
 Battlelore – Khazad-Dûm Pt.2 (Silent Caverns) Lyrics05 junho 2024
Battlelore – Khazad-Dûm Pt.2 (Silent Caverns) Lyrics05 junho 2024
