Malware analysis Malicious activity
Por um escritor misterioso
Last updated 29 maio 2024

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

Brute Force Attacks: Password Protection
Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware: 9781788392501: A,

Learning Malware Analysis: Explore the concepts, tools, and techniques to analyze and investigate Windows malware

Free Cybersecurity Training and Career Development

Malware Analysis: Steps & Examples - CrowdStrike

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis: Steps & Examples - CrowdStrike

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis Benefits Incident Response
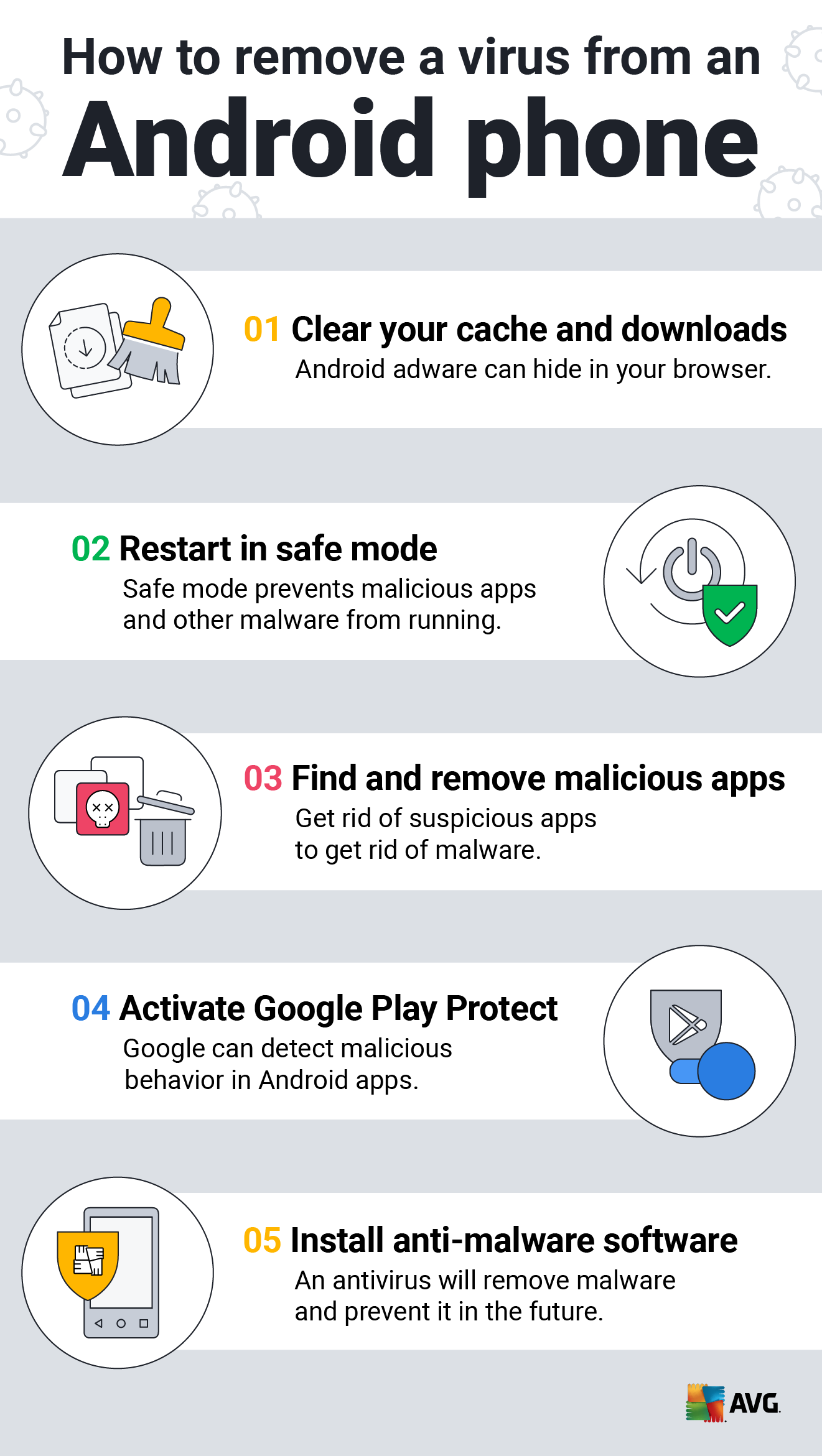
How to Clean an Android or iPhone from Viruses for Free

Endpoint Detection and Response, Free - What is EDR Security?

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
Recomendado para você
-
roblox-cookie-logger · GitHub Topics · GitHub29 maio 2024
-
 Cookie Pool System - Creations Feedback - Developer Forum29 maio 2024
Cookie Pool System - Creations Feedback - Developer Forum29 maio 2024 -
 Roblox Cookie Logger V329 maio 2024
Roblox Cookie Logger V329 maio 2024 -
 What is Cookie Logging? – CrowdStrike29 maio 2024
What is Cookie Logging? – CrowdStrike29 maio 2024 -
 How to remove cookie loggers on roblox29 maio 2024
How to remove cookie loggers on roblox29 maio 2024 -
 Hackers Are Stealing Your Cookies - Panda Security Mediacenter29 maio 2024
Hackers Are Stealing Your Cookies - Panda Security Mediacenter29 maio 2024 -
 i downloaded a roblox COOKIE LOGGER and decided to see what it does29 maio 2024
i downloaded a roblox COOKIE LOGGER and decided to see what it does29 maio 2024 -
Roblox API CSRF token not working only on railway - Railway29 maio 2024
-
cookie logger roblox mobile|TikTok Search29 maio 2024
-
 A Deep Dive into 70 Layers of Obfuscated Info-Stealer Malware29 maio 2024
A Deep Dive into 70 Layers of Obfuscated Info-Stealer Malware29 maio 2024
você pode gostar
-
 Pin em Boards of Love29 maio 2024
Pin em Boards of Love29 maio 2024 -
![The Asgard - Flores [Video oficial] (Prod: FG RECORDS)](https://i.ytimg.com/vi/H3CGqB9T86c/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLA2JpOUF8MPhDuSO-HTJvMd4agUag) The Asgard - Flores [Video oficial] (Prod: FG RECORDS)29 maio 2024
The Asgard - Flores [Video oficial] (Prod: FG RECORDS)29 maio 2024 -
 pre-order Warzone Mobile for free rewards on WZ 2.0! : r/CODWarzone29 maio 2024
pre-order Warzone Mobile for free rewards on WZ 2.0! : r/CODWarzone29 maio 2024 -
 Alphabet Lore X Plushies Stuffed Animal Dolls, Funny Educational29 maio 2024
Alphabet Lore X Plushies Stuffed Animal Dolls, Funny Educational29 maio 2024 -
 Unha tie dye: saiba o que é e como fazer essa unha decorada29 maio 2024
Unha tie dye: saiba o que é e como fazer essa unha decorada29 maio 2024 -
 GameBanshee29 maio 2024
GameBanshee29 maio 2024 -
 Luxury fashion & independent designers, SSENSE29 maio 2024
Luxury fashion & independent designers, SSENSE29 maio 2024 -
 ANIME POWER LEVEL TIER LIST!! (Anime Tier List)29 maio 2024
ANIME POWER LEVEL TIER LIST!! (Anime Tier List)29 maio 2024 -
 CDJapan : Naka no Hito Genome: Jikkyochu Big Key Chain Kaikoku Onigasaki Collectible29 maio 2024
CDJapan : Naka no Hito Genome: Jikkyochu Big Key Chain Kaikoku Onigasaki Collectible29 maio 2024 -
 Custom Falso Coreano Snacks Adereços Modelo, Simulação Comida Hot29 maio 2024
Custom Falso Coreano Snacks Adereços Modelo, Simulação Comida Hot29 maio 2024
