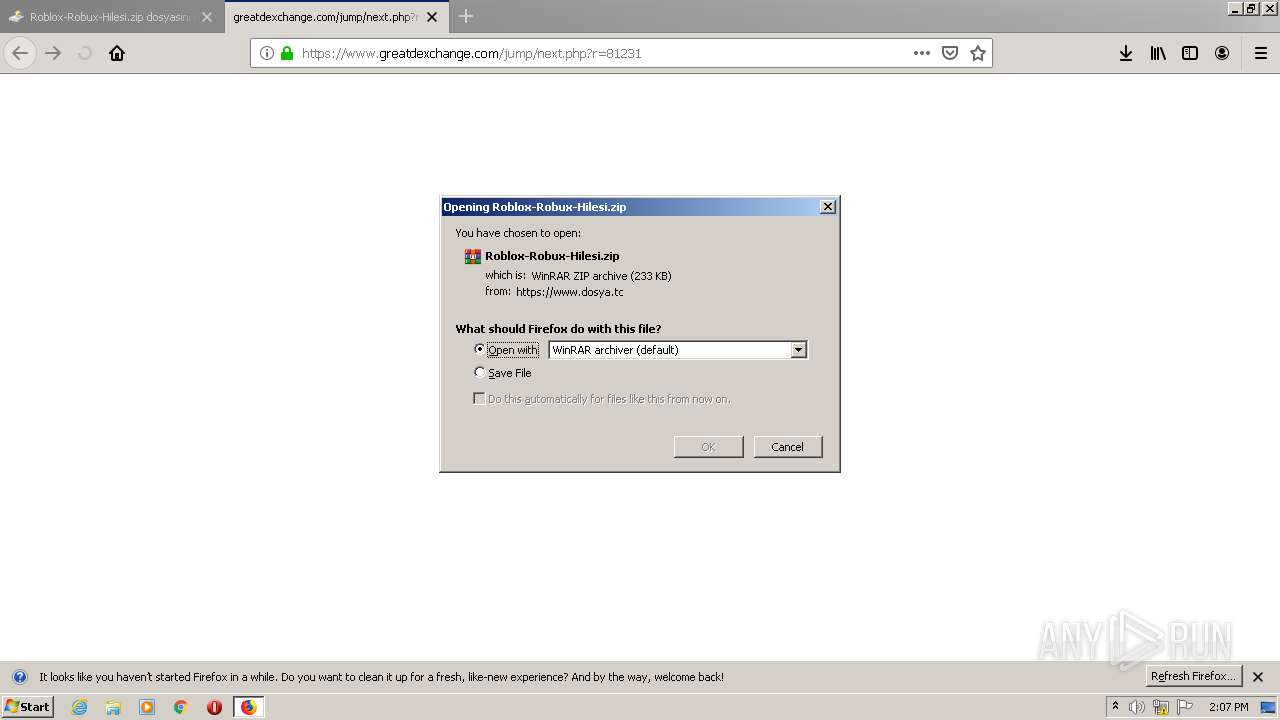
Malware analysis Malicious activity
Por um escritor misterioso
Last updated 10 junho 2024

Malware Analysis: Steps & Examples - CrowdStrike

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Comprehensive Protection Strategies Against Cyber Threats

Info stealers and how to protect against them

Malware analysis AIO_4.9.8__ed.rar Malicious activity

Malware - Wikipedia

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Malware analysis lockysample.bin.zip Malicious activity

Mastering Malware Analysis

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Interactive Online Malware Sandbox

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis index.html Malicious activity

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
Recomendado para você
-
 Roblox::Appstore for Android10 junho 2024
Roblox::Appstore for Android10 junho 2024 -
Roblox Studio for Windows - Download it from Uptodown for free10 junho 2024
-
 ROBLOX 2.605.660 APK for Android - Download - AndroidAPKsFree10 junho 2024
ROBLOX 2.605.660 APK for Android - Download - AndroidAPKsFree10 junho 2024 -
 ROBLOX Mod APK (Unlimited Robux) 2.605.660 Download10 junho 2024
ROBLOX Mod APK (Unlimited Robux) 2.605.660 Download10 junho 2024 -
 MOD-MASTER for Roblox APK Download for Android Free10 junho 2024
MOD-MASTER for Roblox APK Download for Android Free10 junho 2024 -
CO-OWNER - Roblox10 junho 2024
-
 Top 10 Best Android App Store List Alternatives (2023)10 junho 2024
Top 10 Best Android App Store List Alternatives (2023)10 junho 2024 -
Lock Screen For Roblox APK (Android App) - Free Download10 junho 2024
-
 MOD-MASTER for Roblox APK for Android Download10 junho 2024
MOD-MASTER for Roblox APK for Android Download10 junho 2024 -
Download Roblox for android 4.2.210 junho 2024
você pode gostar
-
 Dragon Ball Heroes: anime vai contar com novas Esferas do Dragão - Aficionados10 junho 2024
Dragon Ball Heroes: anime vai contar com novas Esferas do Dragão - Aficionados10 junho 2024 -
 I. Do. Not. Appreciate. Soul. Eater. Not., Gallery posted by Ai Ohto10 junho 2024
I. Do. Not. Appreciate. Soul. Eater. Not., Gallery posted by Ai Ohto10 junho 2024 -
/cdn.vox-cdn.com/uploads/chorus_asset/file/24608446/THEWITCHER_S3_0001.jpg) The Witcher season 3 trailer teases last Henry Cavill Geralt season - Polygon10 junho 2024
The Witcher season 3 trailer teases last Henry Cavill Geralt season - Polygon10 junho 2024 -
 Dragon Ball Z Super Saiyan Majin Vegeta Filho Goku Kakarotto Figura Anime Figma Desktop Modelo Estátua Coleção Brinquedos Para Crianças - Figuras De Ação Militares - AliExpress10 junho 2024
Dragon Ball Z Super Saiyan Majin Vegeta Filho Goku Kakarotto Figura Anime Figma Desktop Modelo Estátua Coleção Brinquedos Para Crianças - Figuras De Ação Militares - AliExpress10 junho 2024 -
 Ludo: Jogue Ludo gratuitamente em LittleGames10 junho 2024
Ludo: Jogue Ludo gratuitamente em LittleGames10 junho 2024 -
 SURVIVAL LIFE (FULL MOVIE) (Minecraft Animation)10 junho 2024
SURVIVAL LIFE (FULL MOVIE) (Minecraft Animation)10 junho 2024 -
 Original stamp Royalty Free Vector Image - VectorStock10 junho 2024
Original stamp Royalty Free Vector Image - VectorStock10 junho 2024 -
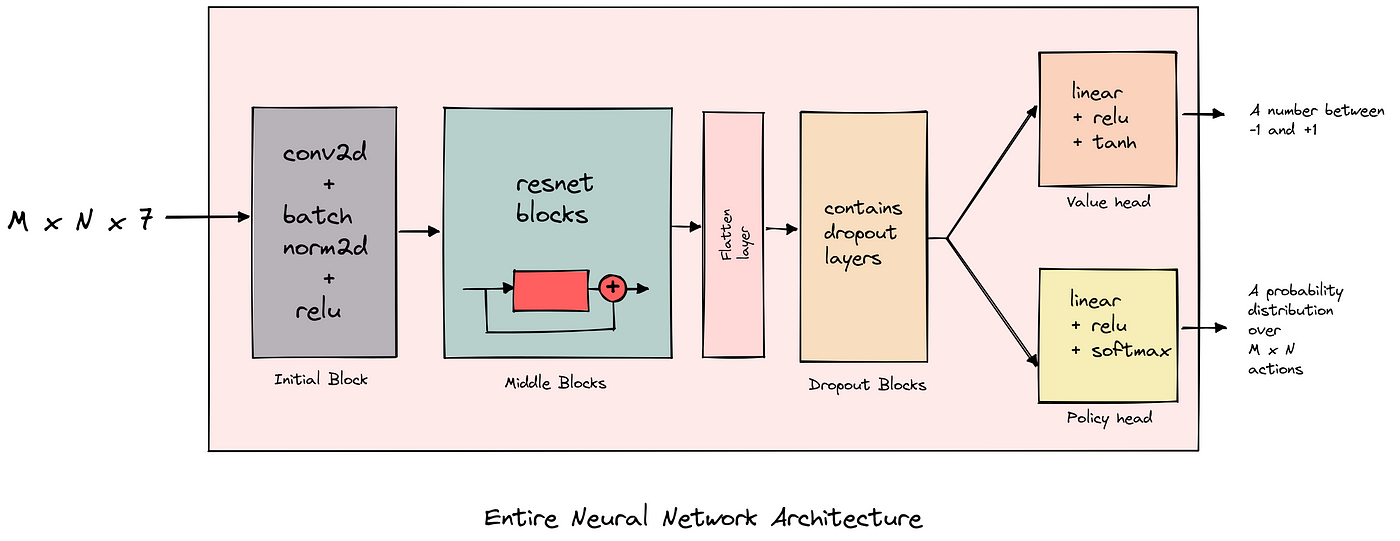 AlphaZero from scratch in PyTorch for the game of Chain Reaction10 junho 2024
AlphaZero from scratch in PyTorch for the game of Chain Reaction10 junho 2024 -
 Hard Reset LENOVO Moto G4 Play10 junho 2024
Hard Reset LENOVO Moto G4 Play10 junho 2024 -
 Anime Can Be Cool: End of Season Review: What Won?10 junho 2024
Anime Can Be Cool: End of Season Review: What Won?10 junho 2024
