Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's Red Team Tools
Por um escritor misterioso
Last updated 17 junho 2024

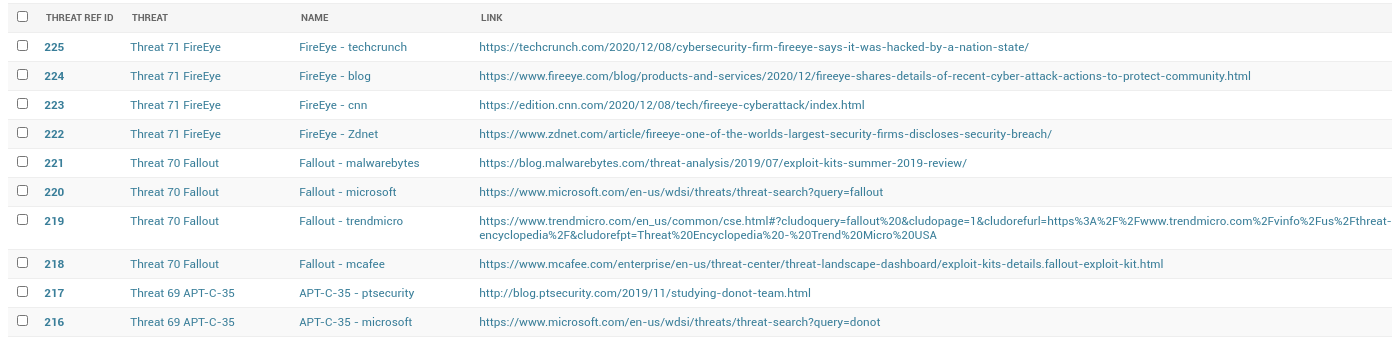
We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
Stamus ND/NDR is Armed to Detect Stolen FireEye Red Team Tools

FireEye, one of the world's largest security firms, discloses

Chinese Cyber Espionage Hackers Continue to Target Pulse Secure

Cyber Security Firm FireEye Reports Major Breach

The five most significant IT security incidents of the last 10

It is Time to Take Action - How to Defend Against FireEye's Red
Stamus ND/NDR is Armed to Detect Stolen FireEye Red Team Tools
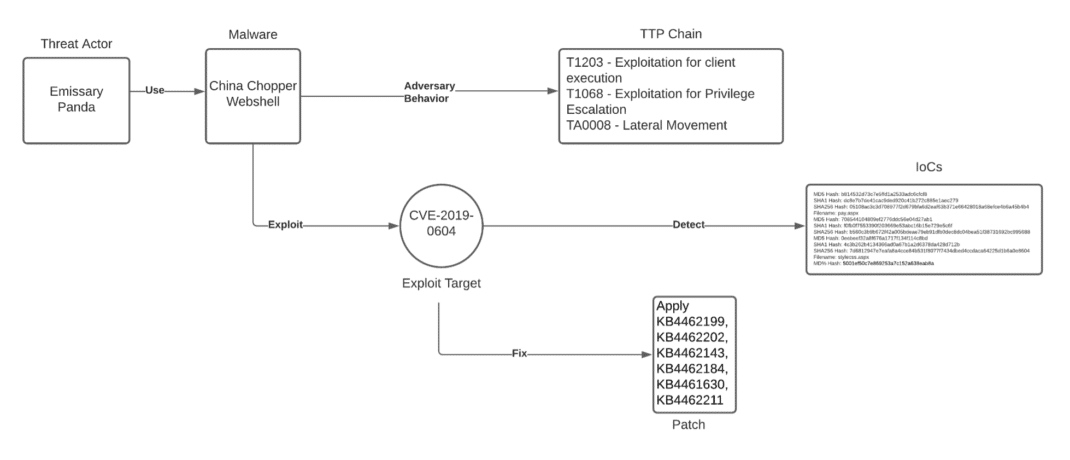
Unpacking the CVEs in the FireEye Breach - Start Here First
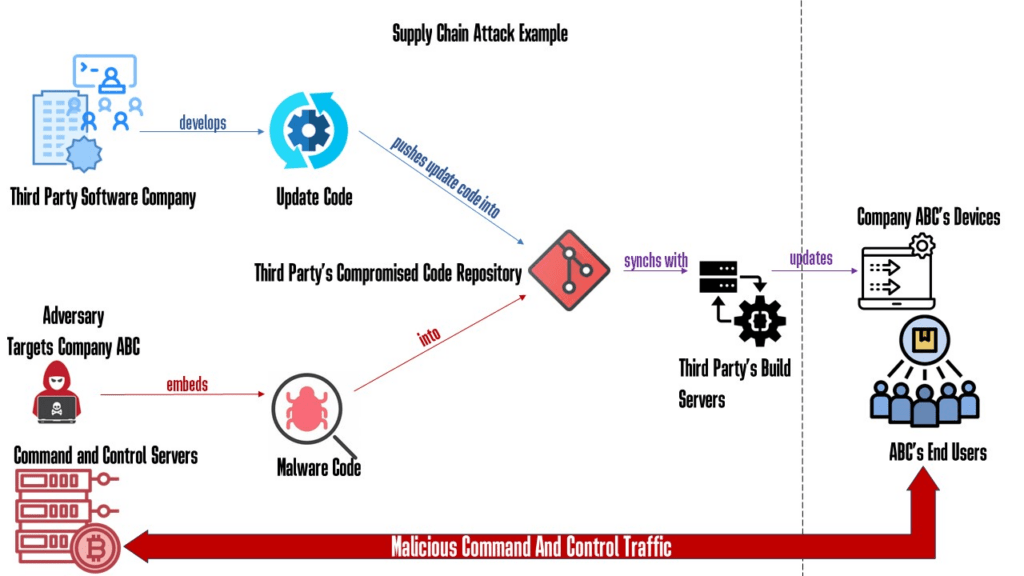
Why Red Teaming Should Be In A Supply Chain Defense Strategy

What are Advance Persistent Threats (APT)?
Recomendado para você
-
 Spoofer Redengine Semanal - Others - DFG17 junho 2024
Spoofer Redengine Semanal - Others - DFG17 junho 2024 -
Raj Echambadi on LinkedIn: Illinois Tech's CARNATIONS Receives $1017 junho 2024
-
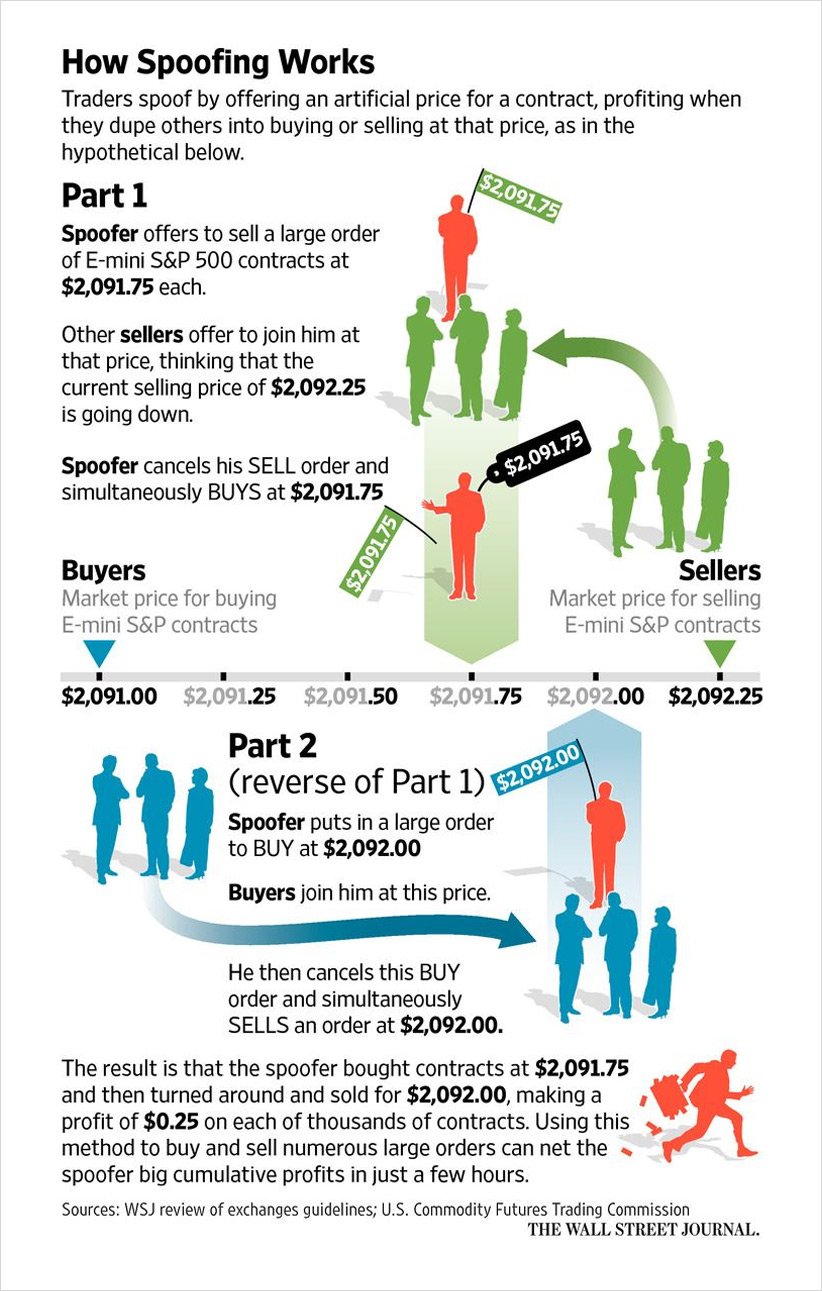 Explaining and Exploring Spoofing - Deribit Insights17 junho 2024
Explaining and Exploring Spoofing - Deribit Insights17 junho 2024 -
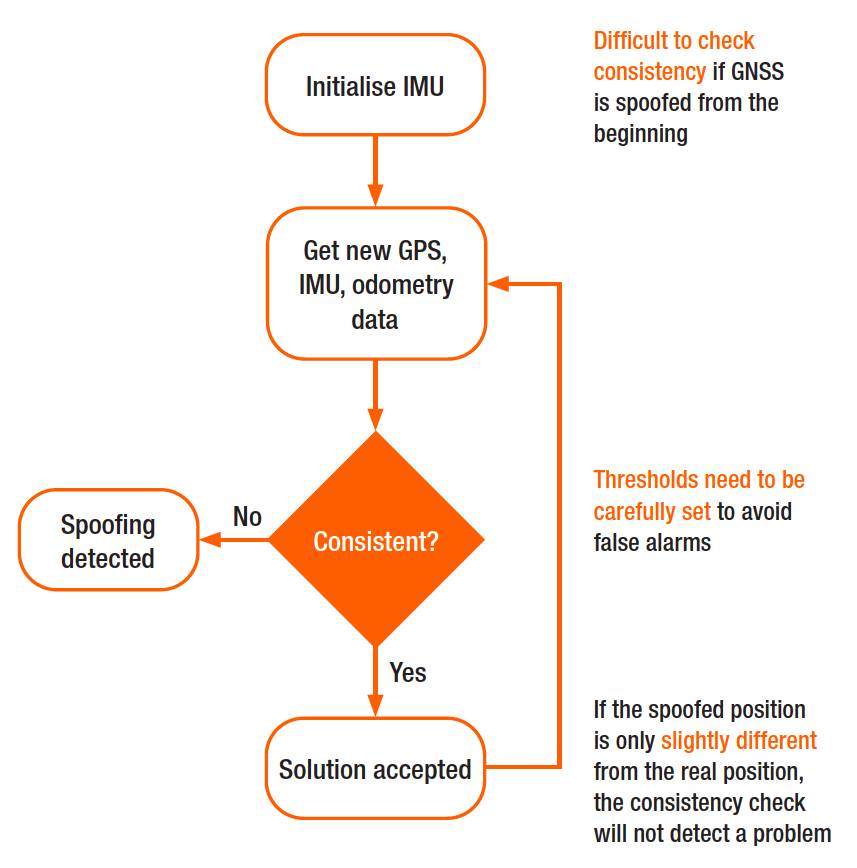 Why secure GPS receivers are crucial for GNSS/INS systems?17 junho 2024
Why secure GPS receivers are crucial for GNSS/INS systems?17 junho 2024 -
 James the Red Engine, Movie Spoof Films Wikia17 junho 2024
James the Red Engine, Movie Spoof Films Wikia17 junho 2024 -
Location Guard17 junho 2024
-
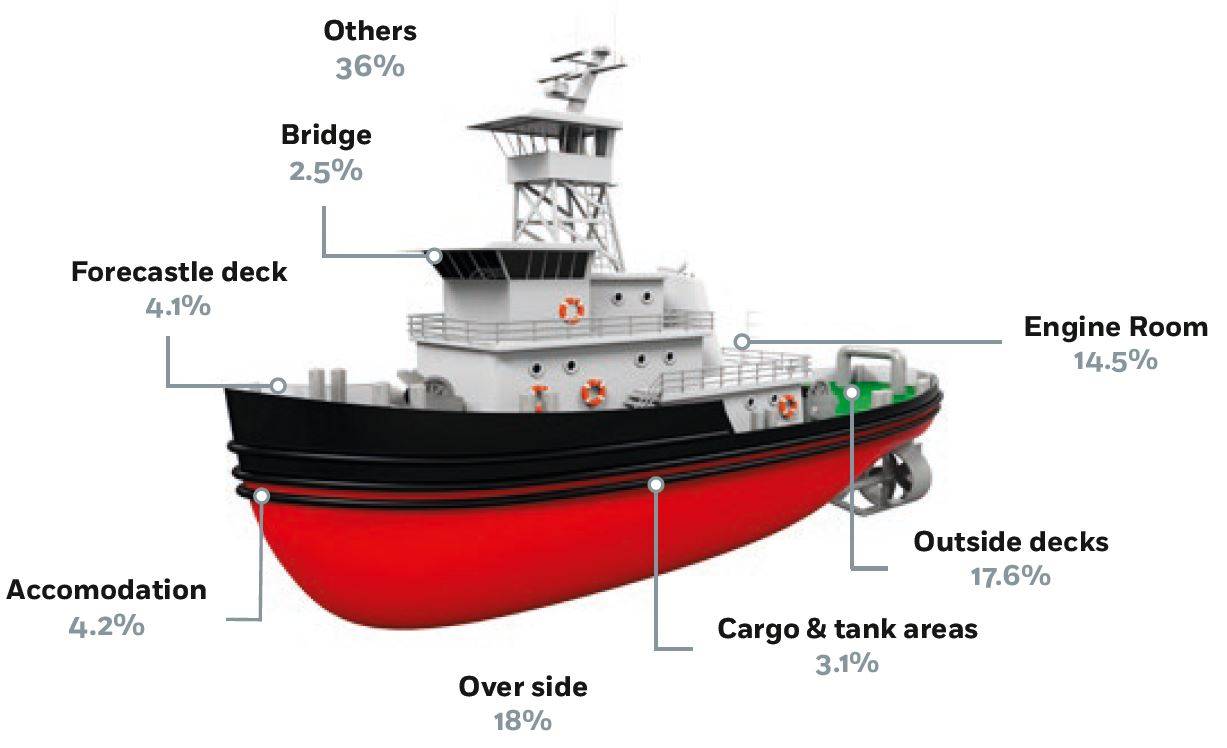 Autonomous Shipping – Cyber Hazards Ahead17 junho 2024
Autonomous Shipping – Cyber Hazards Ahead17 junho 2024 -
 DJ Max Fever - Wikipedia17 junho 2024
DJ Max Fever - Wikipedia17 junho 2024 -
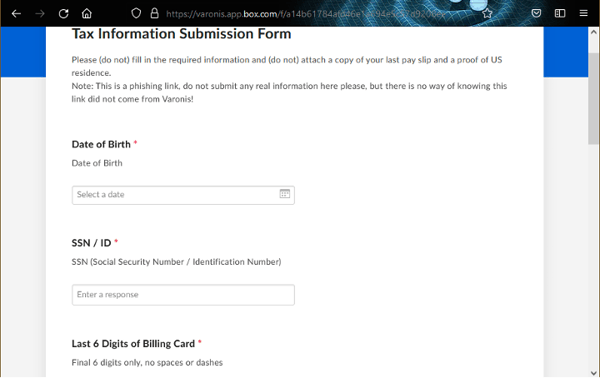 Spoofing SaaS Vanity URLs for Social Engineering Attacks17 junho 2024
Spoofing SaaS Vanity URLs for Social Engineering Attacks17 junho 2024 -
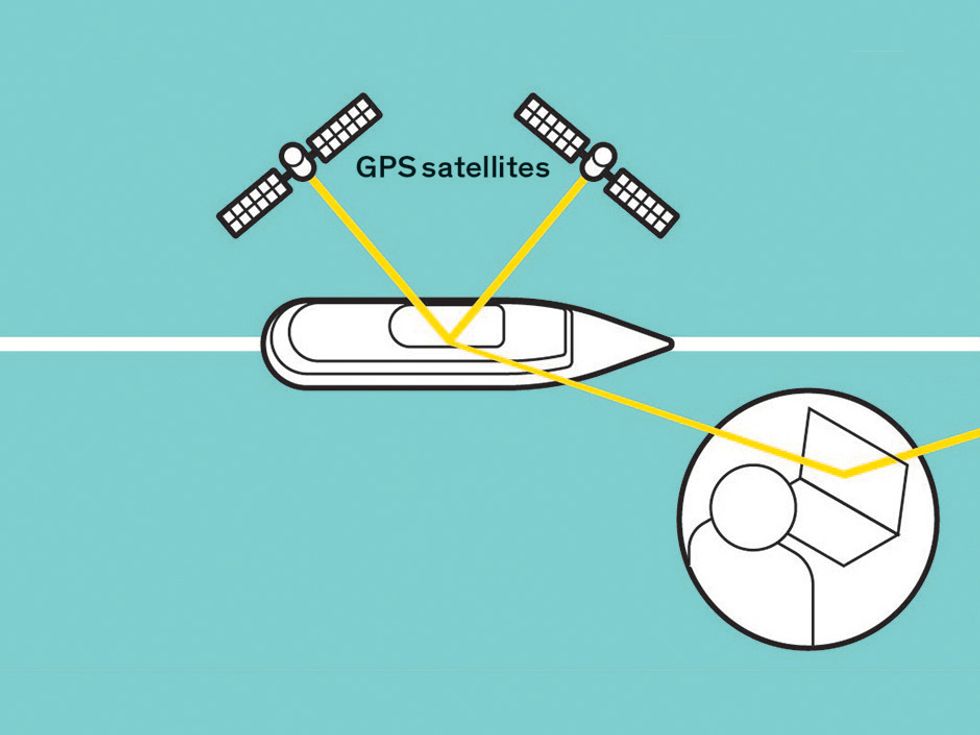 Protecting GPS From Spoofers Is Critical to the Future of17 junho 2024
Protecting GPS From Spoofers Is Critical to the Future of17 junho 2024
você pode gostar
-
 Os 5 Episódios Mais Sinistros de Hora de Aventura17 junho 2024
Os 5 Episódios Mais Sinistros de Hora de Aventura17 junho 2024 -
 Pokémon HOME, Aplicações de download da Nintendo Switch, Jogos17 junho 2024
Pokémon HOME, Aplicações de download da Nintendo Switch, Jogos17 junho 2024 -
Wreckreation - Playstation 5 : Target17 junho 2024
-
 NETHERWORLD presents: Jacob's Ladder at Studio Movie Grill17 junho 2024
NETHERWORLD presents: Jacob's Ladder at Studio Movie Grill17 junho 2024 -
 Another FNAF Blog… Yay on Tumblr - #glamrock bonnie17 junho 2024
Another FNAF Blog… Yay on Tumblr - #glamrock bonnie17 junho 2024 -
NerdiandoX - Simplimente uma lenda. Conhecido como mais homem mais forte do mundo, com poder capaz de destruir o mundo com sua Gura Gura no Mi. Gostou ? Curte e marca uma17 junho 2024
-
Stephen Curry regrets exposing daughter Riley to bright lights17 junho 2024
-
 How To Access Webmail - What Is Webmail? - Knowledge base17 junho 2024
How To Access Webmail - What Is Webmail? - Knowledge base17 junho 2024 -
 10 Hilarious JoJo Part 4 Memes17 junho 2024
10 Hilarious JoJo Part 4 Memes17 junho 2024 -
 Chelsea F.C.–Tottenham Hotspur F.C. rivalry - Wikipedia17 junho 2024
Chelsea F.C.–Tottenham Hotspur F.C. rivalry - Wikipedia17 junho 2024



